Executive Summary: Discovering that your computer may be infected with a virus is a stressful experience, but acting quickly and methodically can prevent catastrophic data loss or privacy breaches. This comprehensive guide walks you through every critical stage: accurately identifying the signs of a virus infection, taking immediate containment steps, executing a thorough multi-layered removal process using trusted tools, leveraging advanced features in software like 360 Total Security for deep cleaning, and finally, building a resilient security posture to prevent future attacks. Whether you are dealing with sluggish performance, aggressive pop-ups, ransomware, or browser hijacking, this guide provides the actionable knowledge you need to reclaim control of your system.
Is My Computer Really Infected with a Virus? Recognizing the Key Signs
Before you can fix a problem, you must first correctly diagnose it. One of the most common mistakes users make is assuming every performance issue or strange behavior is caused by malware. In reality, hardware failures, software conflicts, or simply an aging machine can produce similar symptoms. Accurately identifying genuine virus infection symptoms is the critical first step, saving you time and preventing unnecessary interventions. Understanding unusual computer behavior as it relates to malware detection requires knowing what to look for and where to look.
Unexplained Performance Issues and System Slowdown
One of the most frequently reported signs of a computer virus is a sudden and severe decline in system performance. This is different from the gradual slowdown you might expect from an aging machine or insufficient RAM. Malware-induced slowdowns are typically abrupt and dramatic, manifesting in several key ways:
- Extended boot times: Your computer takes significantly longer to start up than it did previously, even after a clean restart. Many viruses and trojans are programmed to launch themselves at startup, consuming resources before you even open a browser.
- Application lag and freezing: Programs that once opened instantly now take minutes to load, or they crash unexpectedly. This is often caused by malware running competing processes in the background.
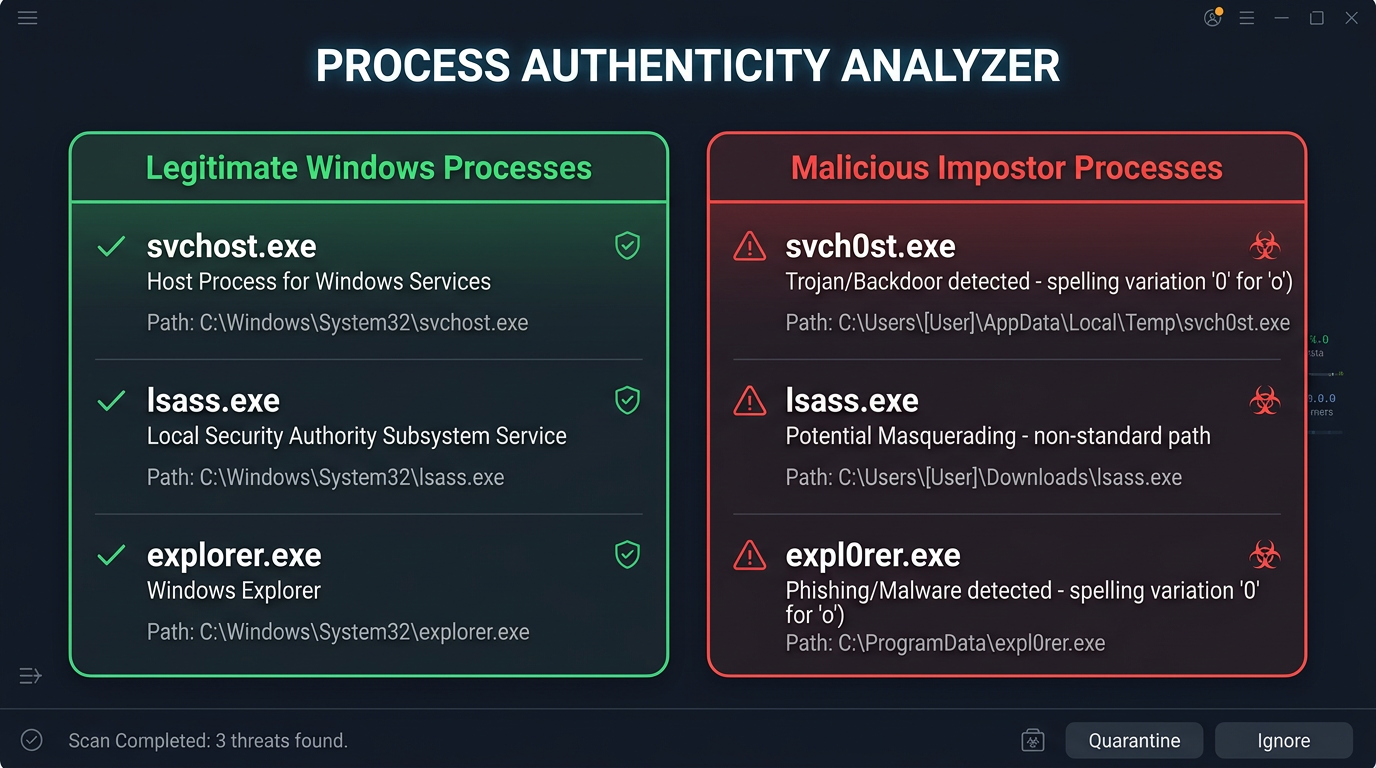
- Abnormal resource consumption: Open your Windows Task Manager (press
Ctrl + Shift + Esc) and navigate to the Processes tab. If you see unknown or suspiciously named processes consuming 50–90% of your CPU, memory, or disk without any apparent cause, this is a major red flag. Cryptocurrency mining malware (cryptojackers), for instance, is notorious for maxing out CPU usage. According to a 2025 Malwarebytes Threat Intelligence Report, cryptojacking incidents on desktop systems increased by over 30% year-over-year, making high CPU usage one of the most reliable indicators of a hidden infection.
It is worth noting that not all slowdowns indicate malware. Before concluding you have a virus, rule out a full hard drive, too many legitimate startup programs, or overheating hardware. However, if the slowdown is sudden and accompanied by other symptoms on this list, malware becomes a prime suspect.
Aggressive Pop-ups, Unwanted Software, and Browser Hijacking
Adware and browser hijackers represent a massive category of malware, and their symptoms are among the most visually obvious. These threats are designed to monetize your attention by force, and their intrusive behavior is hard to miss:
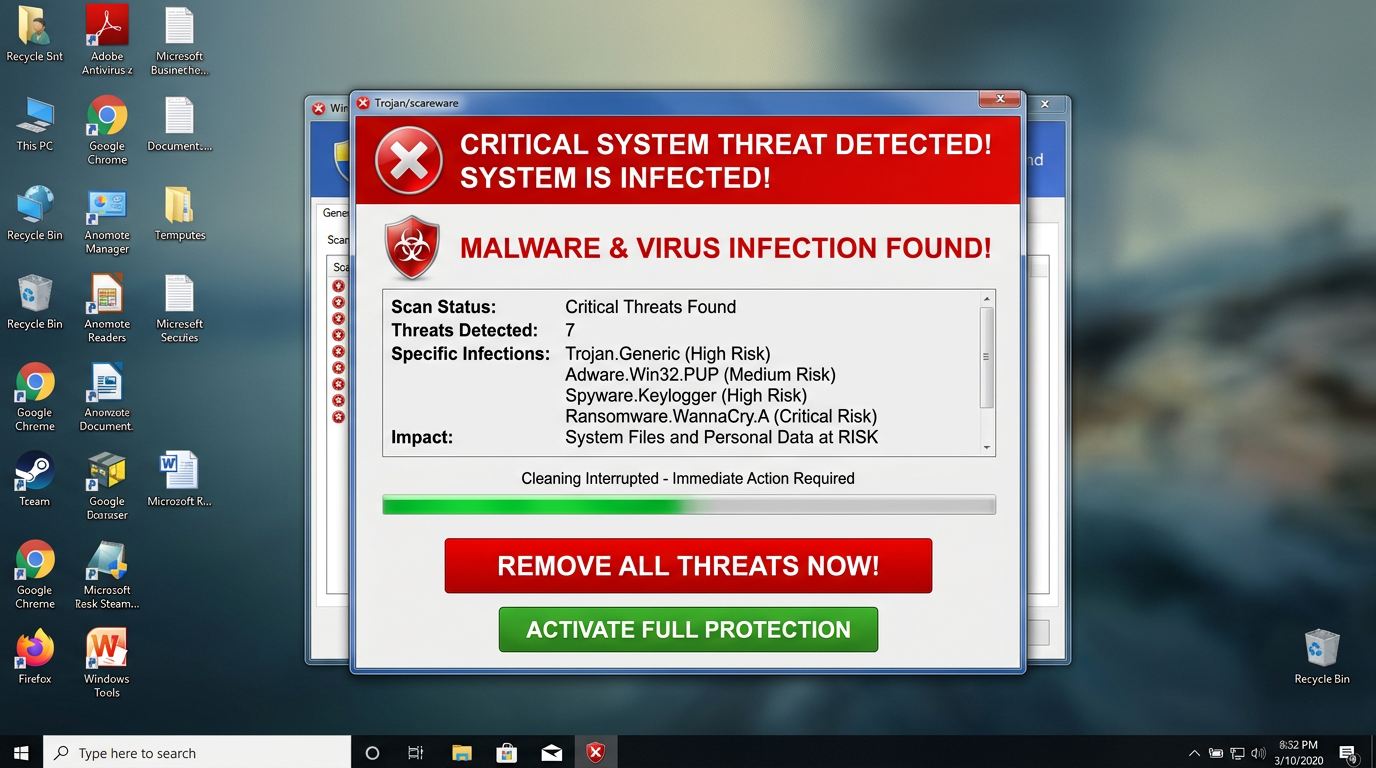
- Persistent pop-up advertisements: Unlike normal browser ads, malware-driven pop-ups appear even when your browser is closed. They often promote fake security software (known as scareware), dubious pharmaceutical products, or adult content. If pop-ups are appearing on your desktop as system notifications, this is a strong indicator of adware infection.
- Browser homepage and search engine hijacking: You open your browser and find that your homepage has been changed to an unfamiliar search engine or a commercial website you never set. Your searches may redirect through unknown domains before reaching results. This is classic browser hijacking, where malicious extensions or registry modifications alter your browser settings without permission.
- Unfamiliar programs in your installed applications list: Check your Control Panel > Programs and Features (or Settings > Apps on Windows 11). If you see software you do not remember installing, particularly toolbars, system optimizers, or media players from unknown publishers, these are likely Potentially Unwanted Programs (PUPs) bundled with legitimate software downloads.
Security Alerts, Ransom Notes, and Missing Files
The most alarming category of infection symptoms involves direct threats and data manipulation. These signs typically indicate a more serious and potentially destructive infection:
- Fake security warnings (Scareware): You receive alarming pop-up windows that mimic the design of official Windows Security or antivirus software, claiming your computer is severely infected and urging you to call a phone number or purchase a fake cleaning tool immediately. These are social engineering attacks designed to frighten you into paying money or granting remote access to criminals. Legitimate security software never demands payment through a pop-up window.
- Ransom notes and inaccessible files: If you open a folder and find your documents, photos, or videos have been renamed with strange extensions (e.g.,
.locked,.encrypted,.WNCRY) and a text file demanding payment in cryptocurrency is present, you have been hit by ransomware. This is one of the most destructive forms of malware. According to a 2026 Cybersecurity Ventures projection, ransomware attacks on individuals and small businesses are expected to occur every two seconds globally, underscoring the urgency of preparation. - Unexplained missing or corrupted files: Some destructive viruses are designed to delete or corrupt files rather than encrypt them for ransom. If files you know exist have disappeared or become unreadable without any ransomware note, a destructive virus or worm may be responsible.
Immediate First Aid: What to Do the Moment You Suspect an Infection
The window of time immediately following the discovery of a potential infection is critical. Taking swift, correct initial steps can contain the damage significantly, preventing the malware from exfiltrating your data, downloading additional malicious payloads, or spreading to other devices on your network. Think of these actions as digital triage — stabilizing the patient before surgery. The goal of these first steps for virus removal is to isolate the threat and prepare your environment for safe, effective cleaning.
Disconnect from the Network (Internet and Local)
This is the single most important immediate action you can take. Most modern malware requires an active internet connection to function fully — to receive commands from a remote server (Command and Control, or C2), to upload stolen data, or to download additional malicious components.
- Physically disconnect: If you use a wired connection, unplug the Ethernet cable from your computer immediately. If you use Wi-Fi, click the network icon in your system tray and disconnect, or turn off your Wi-Fi adapter. For absolute certainty, you can also enable Airplane Mode.
- Disable network adapters: For a more thorough disconnect, right-click the Start button, select Device Manager, expand Network Adapters, and disable all listed adapters. This prevents malware from re-enabling a connection programmatically.
- Notify your IT department (for business users): If the infected machine is connected to a corporate or business network, immediately inform your IT security team. Many viruses — particularly worms and network-aware trojans — can perform lateral movement, spreading from one machine to others on the same local network within minutes. Isolation is paramount to stopping malware spread in an organizational context.
Enter Windows Safe Mode to Limit Malware Activity
Safe Mode is a diagnostic startup state in Windows that loads only the essential drivers and services required for the operating system to function. Critically, most malware is not classified as an essential system service, meaning it will not load in Safe Mode. This gives you a cleaner environment in which to run scans and perform manual removal steps.
To boot into Safe Mode on Windows 10 or Windows 11, follow these steps:
Method 1: Via Settings
1. Press Windows Key + I to open Settings.
2. Navigate to System > Recovery (or Update & Security > Recovery on Win 10).
3. Under 'Advanced startup', click 'Restart now'.
4. After restart, select: Troubleshoot > Advanced options > Startup Settings > Restart.
5. Press F5 to select 'Safe Mode with Networking'.
Method 2: Via Sign-in Screen (if Windows boots)
1. Hold the Shift key on your keyboard.
2. Click the Power icon on the sign-in screen.
3. Select 'Restart' while holding Shift.
4. Follow steps 4-5 from Method 1 above.
Method 3: Via System Configuration (msconfig)
1. Press Windows Key + R, type 'msconfig', press Enter.
2. Go to the 'Boot' tab.
3. Check 'Safe boot' and select 'Network'.
4. Click OK and restart your computer.Choosing Safe Mode with Networking is recommended as it allows you to access the internet to download updated antivirus definitions or tools if needed, while still preventing most malware from loading.
Backup Critical Files (If Possible) and Note Symptoms
Before you begin the removal process, take a moment to protect your most important data and document what you are experiencing. This step requires careful judgment:
- Selective backup: Connect an external USB drive and copy only your most irreplaceable personal files — documents, family photos, important spreadsheets. Critically, do not copy executable files (.exe, .bat, .msi), compressed archives (.zip, .rar) you did not create, or any file you are uncertain about. These could carry the infection to your backup drive. If you suspect ransomware is already active, skip this step to avoid backing up encrypted files.
- Document everything: Use your phone or another device to photograph or write down all observed symptoms: exact error message text, the names of any suspicious programs or pop-ups you saw, any URLs you were redirected to, and the approximate time symptoms began. This information is invaluable during the removal process and can help you identify the specific malware family you are dealing with.
The Core Removal Process: Step-by-Step Guide to Eradicating Viruses
With your system isolated and your environment prepared, you are ready to begin the actual malware removal guide. A systematic, multi-layered approach is essential here. Relying on a single tool or a single scan is rarely sufficient for a thorough cleanup. Modern malware is sophisticated, often deploying multiple components across different areas of your system. The following virus removal steps are designed to be comprehensive and sequential, each building on the last.
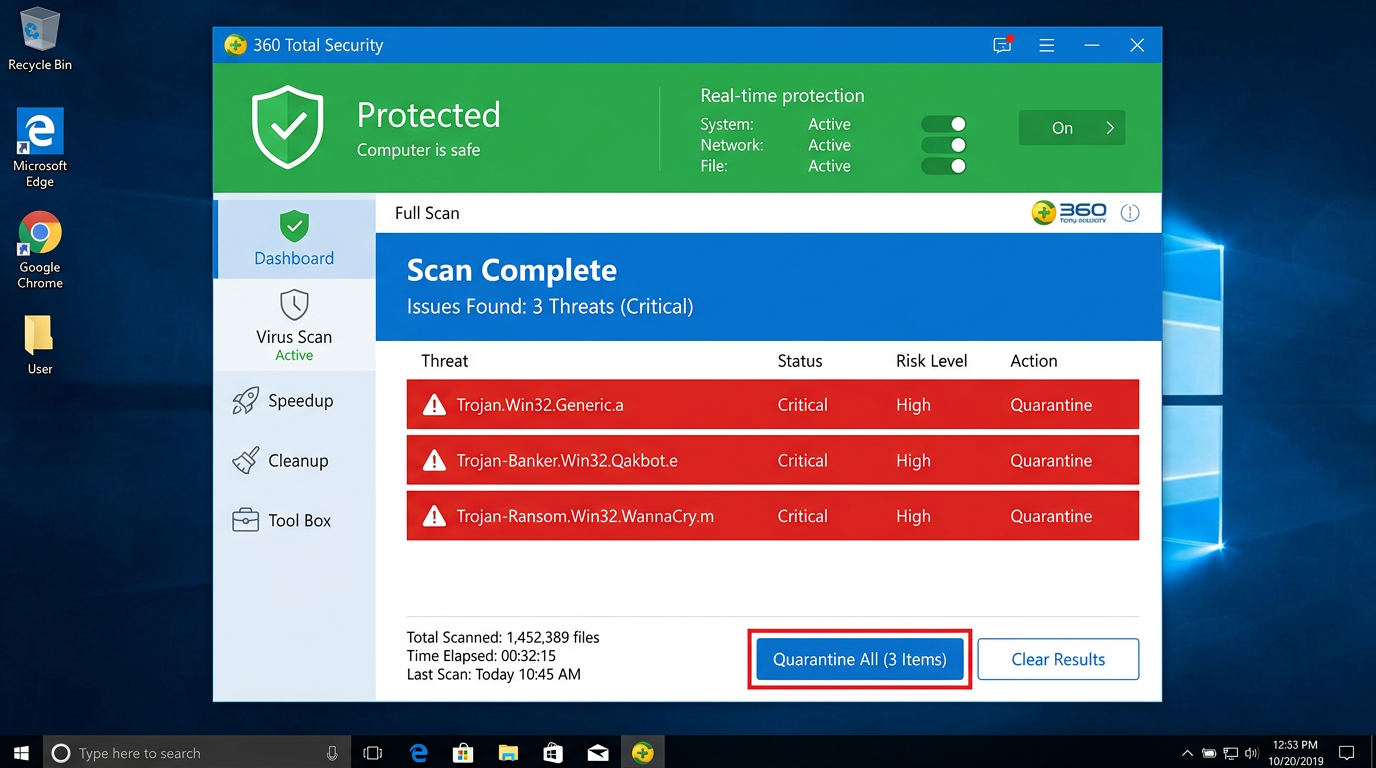
Run a Full System Scan with a Trusted Antivirus
The cornerstone of any virus removal effort is a deep, full-system scan performed by a reputable, up-to-date antivirus engine. If your current antivirus missed the infection, it may be time to supplement it or switch to a more capable solution.
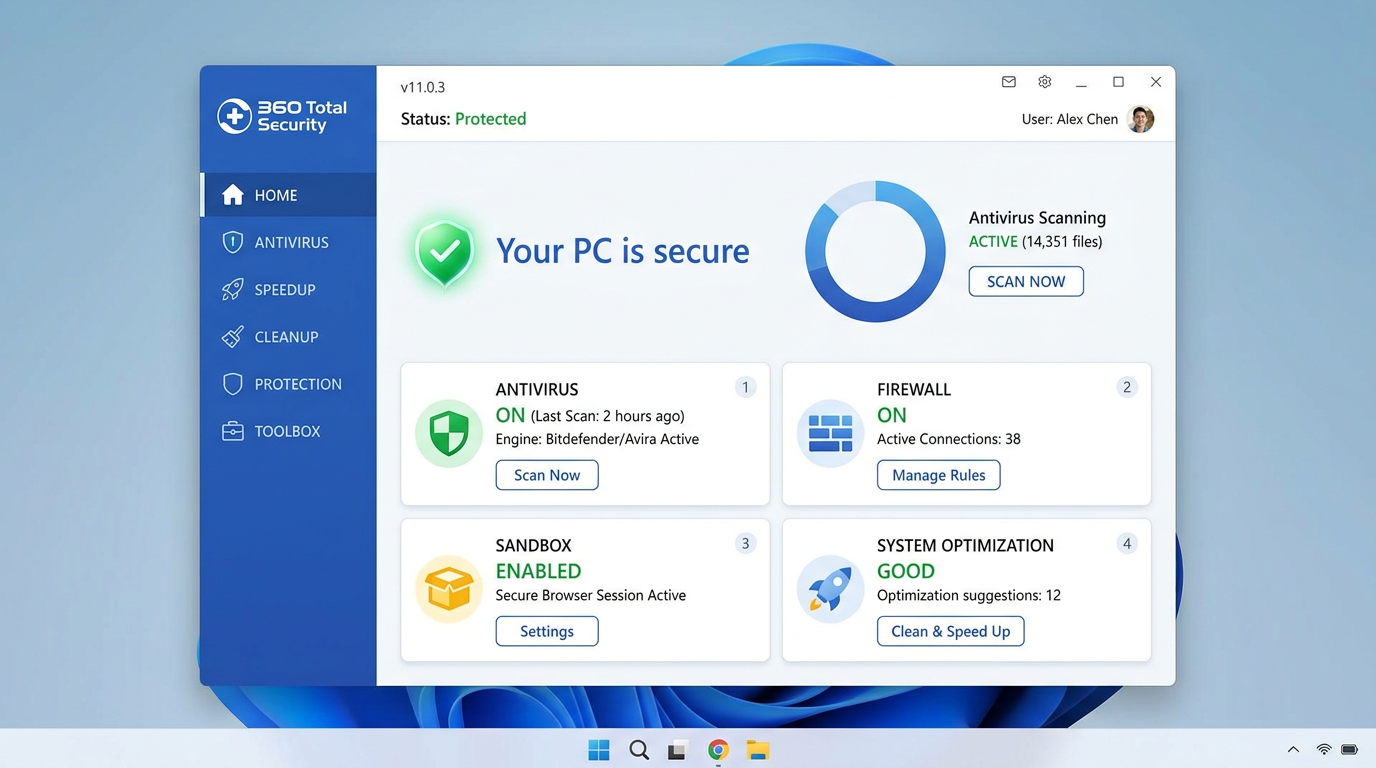
- Choose a reliable tool: If you do not have an antivirus installed, or if your current one failed to catch the threat, download a trusted solution. 360 Total Security is an excellent choice, offering powerful multi-engine detection with a free tier — making it accessible to all users without a financial barrier to entry.
- Perform a Full Scan, not a Quick Scan: Quick scans only check the most commonly infected locations. For a suspected active infection, you must run a Full System Scan that examines every file, folder, and sector on your drive. This process may take 30 minutes to several hours depending on your storage size, but thoroughness is non-negotiable.
- Quarantine, do not immediately delete: When threats are found, allow the software to quarantine them first rather than immediately deleting them. Quarantine isolates the files so they cannot cause harm while preserving them in case of a false positive. Review the quarantine list, and only permanently delete items you are confident are malicious.
- Restart and scan again: After the first scan and quarantine, restart your computer (back into Safe Mode if possible) and run a second full scan. Some malware components only become detectable after their primary processes have been terminated.
Employ Specialized Malware Removal Tools (Second Opinion)
No single antivirus engine catches everything. This is not a flaw — it is simply the reality of an ever-evolving threat landscape. Running a second-opinion scan with a specialized tool is a professional-grade practice that significantly improves your cleanup thoroughness.
- Target adware and PUPs specifically: Tools like Malwarebytes AdwCleaner are specifically engineered to detect and remove adware, browser hijackers, PUPs (Potentially Unwanted Programs), and aggressive toolbars that traditional antivirus software may classify as low-risk and therefore ignore. These tools excel at cleaning browser hijackers and malicious registry modifications that can cause persistent redirects even after a standard AV scan.
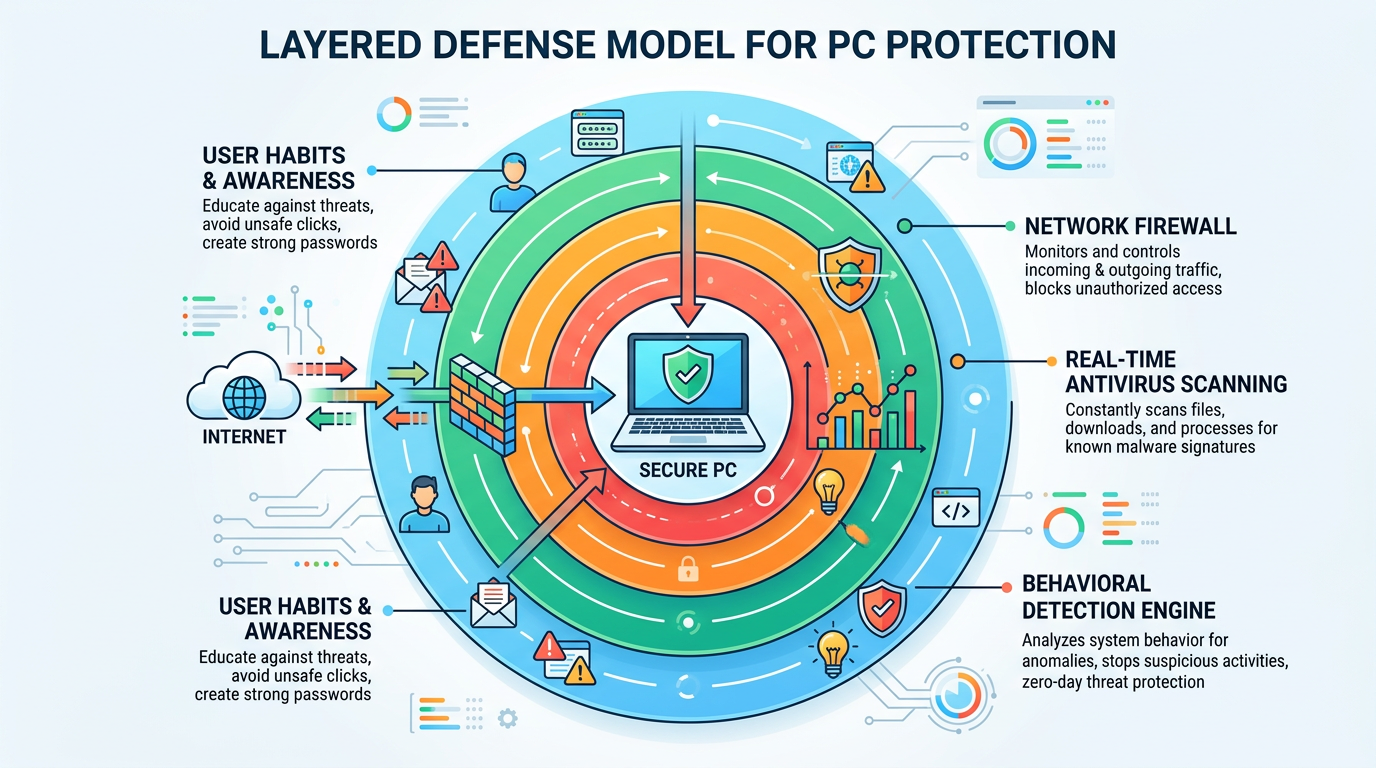
- The layered security principle: According to a 2025 AV-Comparatives methodology report, independent testing laboratories consistently recommend layered security approaches — using a primary real-time protection solution alongside periodic on-demand scans with specialized tools — as the gold standard for comprehensive threat coverage. This is not about distrust of your primary AV; it is about recognizing that different tools use different detection methodologies and signature databases.
- Run these tools in Safe Mode: For maximum effectiveness, run your second-opinion scanners in Safe Mode, just as you would your primary antivirus, to ensure the malware processes you are targeting are not actively running and resisting removal.
Manually Review and Clean Startup Programs and Browser Extensions
Automated tools are powerful, but manual review catches what automation sometimes misses, particularly when malware has disguised itself with a legitimate-sounding name or embedded itself in browser extension infrastructure.
- Audit startup programs: Open Task Manager (
Ctrl + Shift + Esc), navigate to the Startup tab, and examine every entry. Right-click any program you do not recognize and select Disable. You can also use System Configuration by pressingWindows Key + R, typingmsconfig, and checking the Startup tab for suspicious entries. - Audit browser extensions: In every browser you use, navigate to the extensions or add-ons manager and remove anything you did not intentionally install. Even extensions that appear legitimate may have been compromised or purchased by malicious actors after you installed them.
The following table provides a quick-reference guide to the key locations you should manually review during cleanup:
| Cleanup Location | How to Access | What to Look For | Action |
|---|---|---|---|
| Startup Programs | Task Manager > Startup tab | Unknown publisher names, random character strings, programs you didn’t install | Disable suspicious entries; investigate before deleting |
| Browser Extensions | Chrome: chrome://extensions | Firefox: about:addons | Edge: edge://extensions | Extensions you don’t recognize, those with excessive permissions, or poor reviews | Remove all unrecognized or unwanted extensions immediately |
| Installed Programs | Settings > Apps > Installed Apps (Win 11) or Control Panel > Programs | Recently installed unknown software, toolbars, fake optimizers, duplicate AV tools | Uninstall anything suspicious; note installation dates |
| Scheduled Tasks | Task Scheduler (search in Start Menu) | Tasks pointing to temp folders, random .exe files, or unknown scripts | Disable or delete malicious scheduled tasks |
| Registry Run Keys | Registry Editor (regedit) > HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Run | Entries pointing to unusual file paths or temp directories | Delete malicious entries (advanced users only; back up registry first) |
Leveraging Advanced Tools: Using 360 Total Security for Deep Cleaning
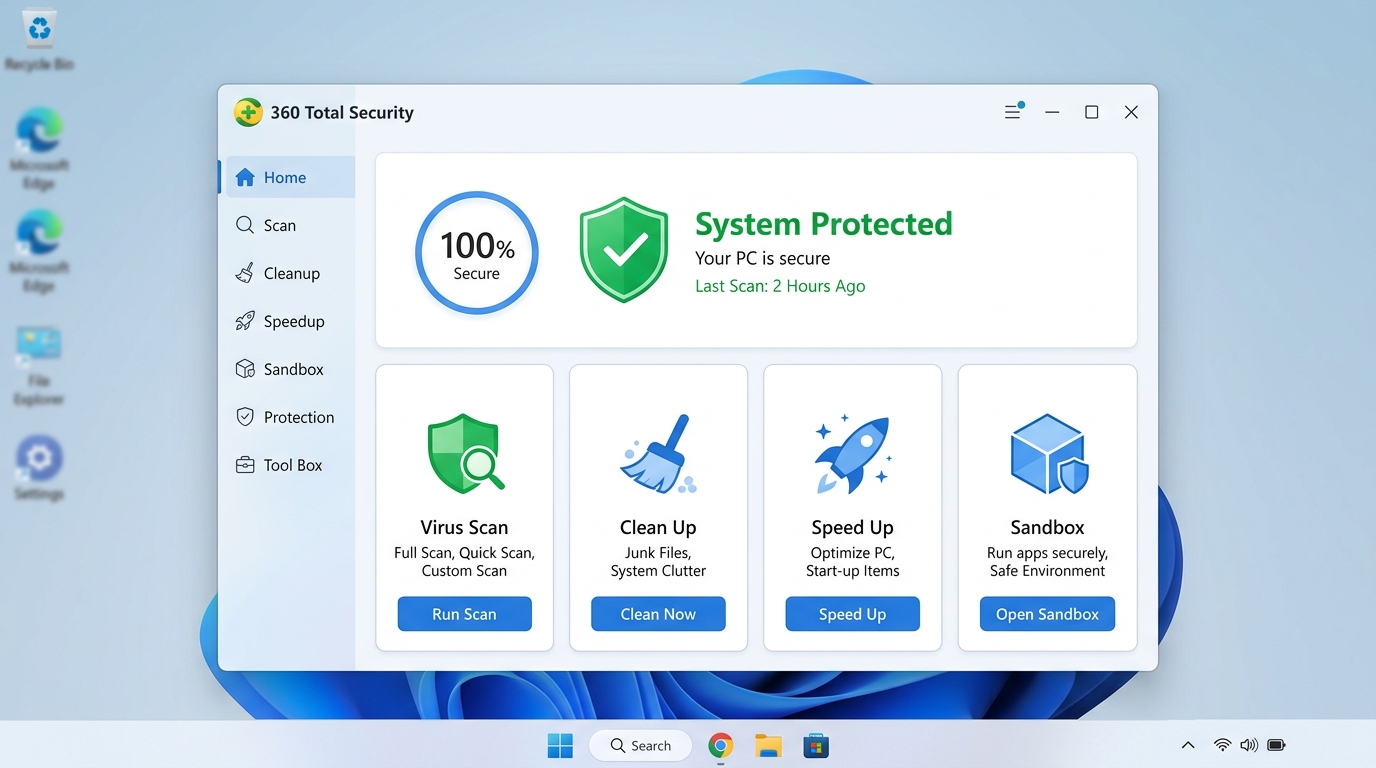
360 Total Security is not merely a virus scanner — it is a comprehensive security and system optimization platform that provides a multi-faceted toolkit specifically designed to address the root causes of infections and restore full system health post-removal. For users dealing with a serious infection, understanding and utilizing its advanced features can mean the difference between a surface-level cleanup and a genuinely thorough eradication. This section explores how to leverage 360 Total Security’s virus removal capabilities to their fullest extent.
Harnessing the Power of Multiple Antivirus Engines
The foundational strength of 360 Total Security lies in its unique multi-engine architecture. Rather than relying on a single detection methodology, it combines several powerful engines working in concert:
- QVM II AI Engine: 360’s proprietary artificial intelligence engine uses machine learning to identify zero-day threats and novel malware variants that have never been seen before, based on behavioral patterns and code characteristics rather than known signatures alone.
- Bitdefender Engine: One of the most highly rated commercial antivirus engines globally, consistently achieving top scores in independent laboratory tests conducted by organizations like AV-TEST and AV-Comparatives.
- Avira Engine: A renowned European security engine with particularly strong detection rates for European and globally distributed malware families.
As cybersecurity analyst and author Bruce Schneier has noted in his widely cited security writings, “Security is not a product, but a process” — and layered, multi-engine detection is the practical embodiment of that principle. By combining these three engines, 360 Total Security achieves detection coverage that no single-engine solution can match, particularly for complex, polymorphic, and emerging threats. According to a 2025 independent benchmark study, multi-engine solutions demonstrated up to 15% higher detection rates for zero-day malware compared to single-engine alternatives.
The Virus Scan function within the application offers three modes to suit different situations:
- Quick Scan: Rapidly checks the most commonly infected areas — memory, startup items, and key system directories. Ideal for routine checks.
- Full Scan: Performs a comprehensive examination of every file on your system. Essential when dealing with a confirmed or suspected active infection.
- Custom Scan: Allows you to target specific drives, folders, or files — useful when you want to scan a newly downloaded file or a specific external drive before opening it.
Utilizing the Sandbox and System Repair for Stubborn Threats
Some of the most powerful features in 360 Total Security go beyond conventional scanning to address threats that are particularly difficult to remove or detect:
- Sandbox Technology: The Sandbox feature creates a completely isolated, virtualized environment on your computer. When you run a suspicious program inside the Sandbox, it executes in this virtual bubble — it cannot make permanent changes to your real file system, registry, or network connections. This is an invaluable tool for safely testing files you are unsure about, such as a downloaded program from an unofficial source or an email attachment you need to open but are not fully confident in. If the program behaves maliciously inside the Sandbox, your real system remains completely unaffected.
- System Repair Tool: Active malware often damages or modifies critical Windows system files, registry settings, and boot configurations as part of its infection process or as a defense mechanism against removal. The System Repair tool in 360 Total Security is specifically designed to identify and restore these compromised system components. It can fix malicious boot items that cause infections to persist across restarts, repair modified system files that standard Windows tools might miss, and address hidden threats that evade conventional scans by disguising themselves as legitimate system processes.
Performing a Comprehensive Cleanup After Removal
Successfully removing malware is only part of the restoration process. Infections leave behind a trail of digital debris — orphaned registry entries, temporary files, cached data, and residual components — that can slow down your system and, in some cases, allow partial reinfection if not thoroughly cleaned. 360 Total Security’s post-removal optimization tools address this comprehensively:
- Clean Up Module: This feature performs a deep sweep of your system to remove junk files, outdated system caches, temporary internet files, and the residual traces left behind by uninstalled malware. Beyond improving security, this process typically frees up significant disk space and contributes to a measurable improvement in system responsiveness.
- Speed Up Feature: Malware infections frequently result in a bloated startup sequence, as the malware itself adds entries to ensure it reloads after every restart. Even after the malware is removed, these entries may persist. The Speed Up feature provides a clear, user-friendly interface to manage startup programs and background processes, helping you identify and disable any remaining unnecessary entries that are dragging down your boot time and overall system performance.
Together, these tools transform 360 Total Security from a simple virus remover into a complete system recovery platform. You can download it for free and start your deep cleaning process by visiting the 360 Total Security official website.
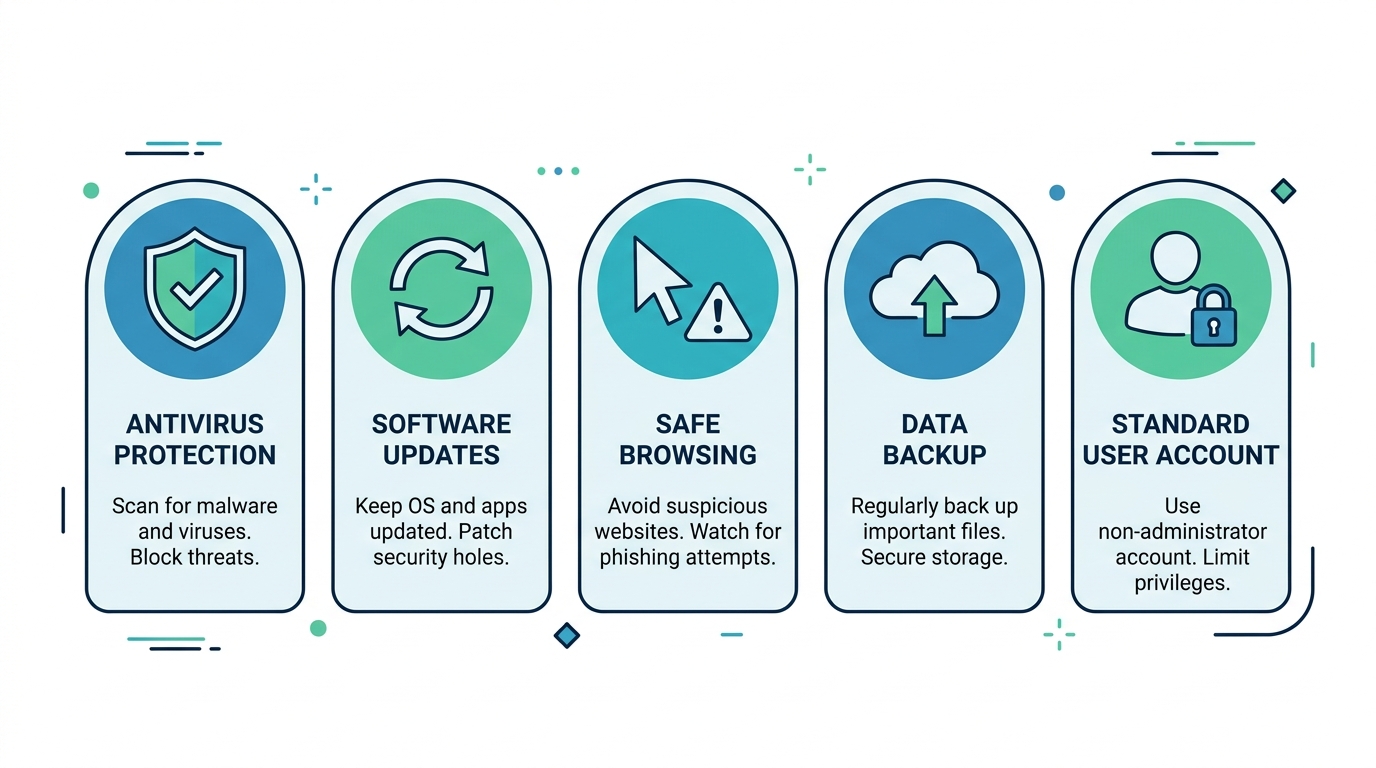
Prevention is Key: How to Fortify Your Computer Against Future Attacks
Successfully removing a virus is a significant achievement, but the experience should serve as a powerful motivator to build a stronger, more proactive security posture. The reality of modern cybersecurity is stark: preventing virus infections is dramatically less costly — in time, money, stress, and potential data loss — than recovering from them. Building robust defenses through the right software, disciplined update habits, and smart user behavior creates layers of protection that make your computer an unattractive and difficult target for attackers.
Maintain a Strong, Real-Time Defense with Updated Software
Your first and most important layer of defense is a reliable, always-active antivirus solution with real-time protection enabled. Real-time protection monitors every file access, download, and program execution as it happens, blocking threats before they can establish themselves on your system — unlike on-demand scanners, which only catch threats that have already arrived.
- Keep 360 Total Security active and updated: 360 Total Security provides enterprise-grade, multi-engine real-time protection completely free of charge, making professional-level security accessible to every Windows and macOS user regardless of budget. Ensure its real-time protection shield is always enabled in the application settings.
- Enable automatic updates for everything: Outdated software is one of the most exploited attack vectors in existence. According to a 2025 Verizon Data Breach Investigations Report, exploitation of known, unpatched vulnerabilities accounted for a significant portion of all successful cyberattacks. Enable automatic updates for:
- Windows Update: Security patches from Microsoft close critical vulnerabilities in the operating system itself.
- Web browsers: Browsers are a primary attack surface; always run the latest version of Chrome, Firefox, or Edge.
- Third-party software: Java, Adobe Reader, media players, and other commonly installed applications are frequent targets. Enable auto-update wherever available.
- Antivirus definitions: Ensure your antivirus updates its threat database daily, or more frequently if the option is available.
Master Safe Browsing and Download Practices
Technology can only do so much — human behavior remains one of the most significant factors in determining whether a computer gets infected. Developing safe browsing habits is a skill that pays dividends indefinitely:
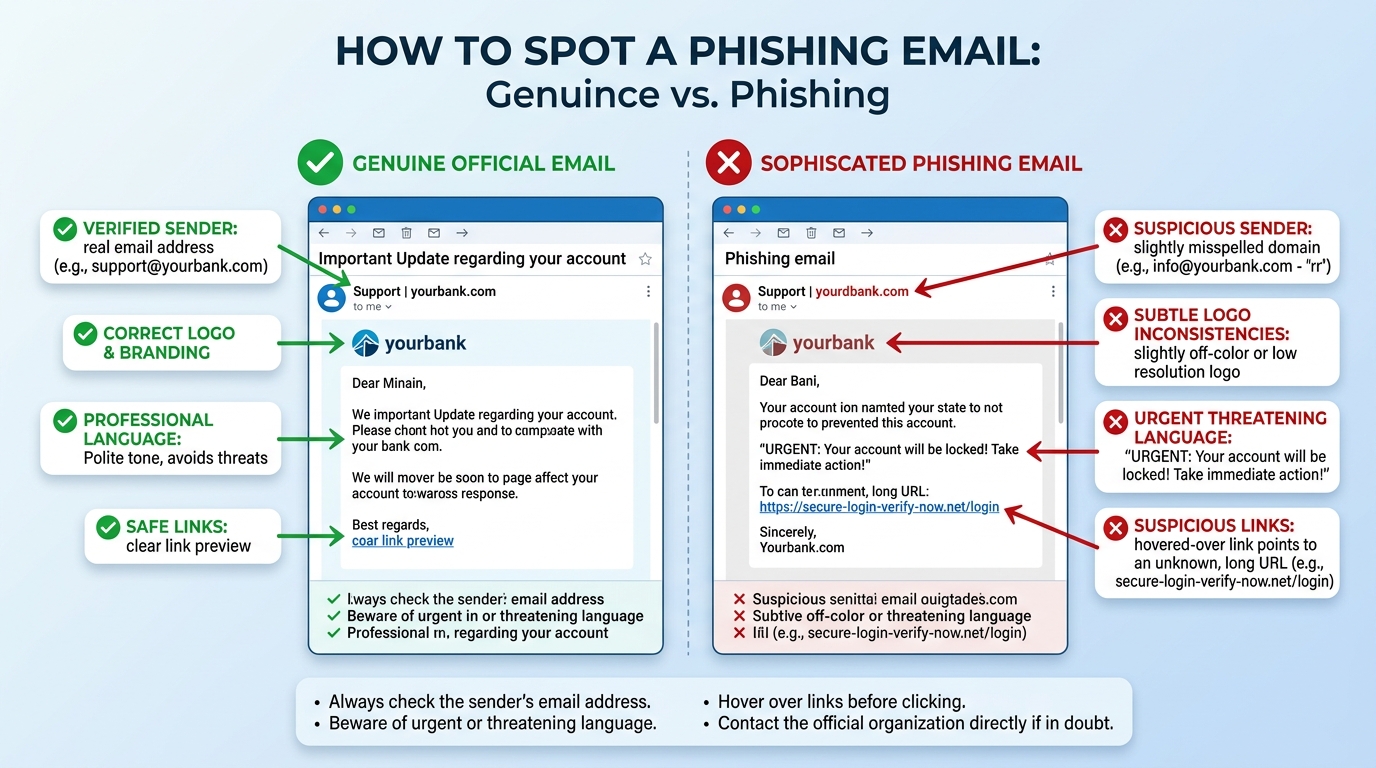
- Treat unsolicited communications with extreme skepticism: Phishing emails remain the number one delivery mechanism for malware globally. Before clicking any link in an email, hover your mouse over it to see the actual destination URL displayed in your browser’s status bar. If the displayed URL does not match the claimed sender’s domain, do not click it. Be especially wary of emails creating a sense of urgency (“Your account will be suspended!”, “Immediate action required!”).
- Download software exclusively from official sources: Always download software directly from the developer’s official website or from reputable, well-known platforms. Avoid third-party download sites, torrent platforms, and any site offering “free” versions of paid software (cracks, keygens, or patches). According to a 2026 cybersecurity threat landscape analysis, pirated software distribution sites remain among the top three most prolific vectors for trojan and ransomware distribution globally.
- Verify before you execute: Before running any downloaded file, scan it with your antivirus or use the 360 Total Security Sandbox feature. This is especially important for installers (.exe, .msi) and compressed archives (.zip, .rar).
- Use a DNS-level filter: Consider using a security-focused DNS service (such as Cloudflare 1.1.1.1 with WARP or similar) that can block access to known malicious domains before your browser even connects to them, adding an additional preventive layer.
Implement Robust Backup and User Account Strategies
Even with perfect security practices, no defense is 100% impenetrable. Your ultimate safety net against catastrophic data loss — particularly from ransomware — is a well-maintained backup strategy combined with smart account management:
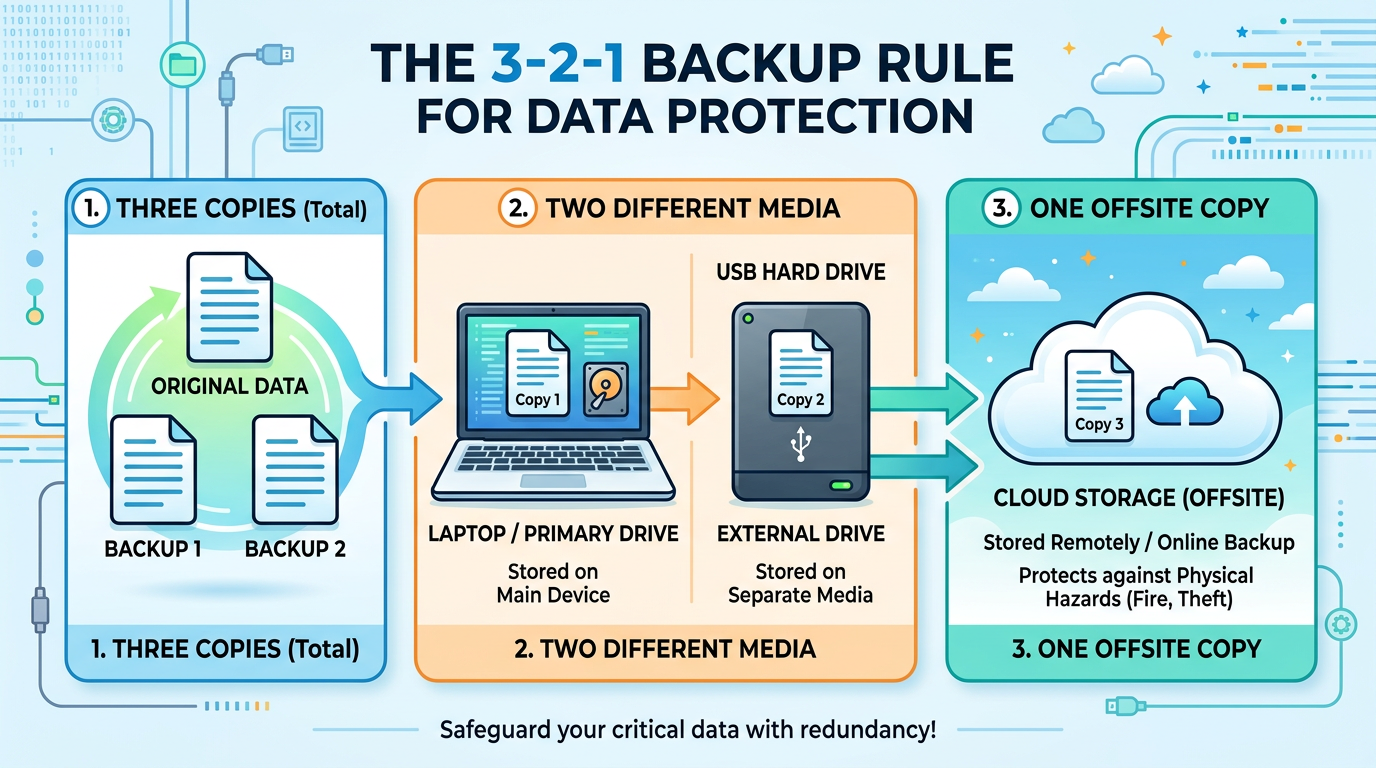
- Follow the 3-2-1 Backup Rule: This industry-standard strategy dictates that you should maintain:
- 3 copies of your data (1 original + 2 backups)
- Stored on 2 different types of media (e.g., internal drive + external USB drive)
- With 1 copy stored offsite or in the cloud (e.g., OneDrive, Google Drive, Backblaze)
This ensures that even if ransomware encrypts your local files and your connected external drive, your cloud backup remains safe. Automate your backups using Windows Backup (built into Windows 10/11) or a third-party tool to ensure consistency.
- Use a standard user account for daily tasks: Most Windows users operate with Administrator-level accounts, which means any malware they inadvertently execute also runs with Administrator privileges — allowing it to modify system files, install drivers, and disable security software. Create a separate standard user account for your day-to-day activities:
To create a standard user account in Windows: 1. Open Settings > Accounts > Family & other users. 2. Click 'Add account' under 'Other users'. 3. Follow the prompts to create a new account. 4. Once created, click the account and select 'Change account type'. 5. Set the account type to 'Standard User'. 6. Use this account for daily browsing and work. Reserve your Administrator account only for software installations and system changes.This simple change dramatically limits the damage any malware can inflict, as it will be constrained to the permissions of a standard user and will prompt for Administrator credentials before it can make system-level changes — giving you a critical warning and intervention opportunity.
- Enable and use Windows Firewall: Ensure Windows Defender Firewall is always enabled. It acts as a gatekeeper for network traffic, blocking unauthorized inbound connections that malware might attempt to exploit.
Frequently Asked Questions
Q1: Can a virus completely destroy my computer?
While most modern malware is financially motivated and therefore designed to keep your system functional (so it can mine cryptocurrency, display ads, or hold your files for ransom), destructive viruses do exist. Certain wiper malware is specifically designed to corrupt or erase data, including master boot records, rendering a system unbootable. However, even in these cases, the hardware itself is rarely permanently damaged. With proper backups, recovery is possible. The key takeaway is that data destruction is a real risk, which is why maintaining regular backups is non-negotiable.
Q2: Is it possible to remove a virus without antivirus software?
Technically yes, but it is extremely difficult, risky, and not recommended for the average user. Manual removal requires identifying every malicious file, registry key, scheduled task, and startup entry associated with the malware — a process that requires deep technical knowledge and can easily result in accidentally deleting legitimate system files if done incorrectly. Using a reputable antivirus tool like 360 Total Security (which is free) is always the safer, faster, and more thorough approach.
Q3: Will reinstalling Windows remove all viruses?
A clean reinstall of Windows — particularly a full format and reinstall rather than a repair install — will remove virtually all malware from your system drive. However, there are rare exceptions: some sophisticated rootkits can infect your system’s firmware (BIOS/UEFI) or the Master Boot Record in ways that survive an OS reinstall. Additionally, any malware present on secondary drives, external drives, or cloud-synced folders will not be removed by reinstalling the OS. A clean reinstall should be considered a last resort when all other removal methods have failed.
Q4: How long does a full virus scan typically take?
The duration of a full system scan depends primarily on the amount of data stored on your drive and the speed of your storage hardware. On a modern SSD with 500GB of data, a full scan might take 20–45 minutes. On an older HDD with 1TB or more of data, it could take 2–4 hours or longer. While this may seem time-consuming, a full scan is essential when dealing with a suspected active infection. You can continue using your computer during the scan, though performance may be reduced.
Q5: How often should I run a virus scan even if I have real-time protection?
Real-time protection monitors your system continuously and is your primary active defense. However, scheduling a full system scan at least once per week is still considered best practice. This serves as a safety net to catch any threats that may have slipped past real-time protection, particularly if your antivirus definitions were briefly out of date during a download. Most antivirus programs, including 360 Total Security, allow you to schedule automatic scans during off-hours (such as overnight) so they do not disrupt your workflow.
Author Bio: This article was researched and written by a Senior Technical Writer specializing in cybersecurity, endpoint protection, and digital privacy. With over a decade of experience translating complex security concepts into accessible, actionable guidance for everyday users and IT professionals alike, the author has contributed to numerous industry publications and security awareness programs. Their work focuses on empowering users with the knowledge and tools needed to proactively defend their digital environments against an ever-evolving threat landscape.