Executive Summary: The belief that Mac computers are completely immune to viruses is one of the most persistent and dangerous myths in consumer technology. While macOS does offer robust architectural advantages over some competing platforms, modern cybercriminals have adapted their tactics, producing a rapidly expanding ecosystem of Mac-specific malware, adware, ransomware, and spyware. This comprehensive guide dismantles the immunity myth with documented evidence, explains precisely how Macs get infected, identifies the warning signs of a compromised system, and delivers a structured, layered defense strategy — including how dedicated solutions like 360 Total Security elevate your protection beyond what Apple’s built-in tools alone can provide.
Debunking the Myth: Are Mac Computers Truly Immune to Viruses?
For decades, the idea that Macs simply do not get viruses has been treated as common knowledge — repeated in coffee shops, corporate IT corridors, and Apple marketing materials alike. The reality in today’s threat landscape is far more nuanced and considerably more alarming. While macOS possesses genuine security advantages rooted in its architecture and ecosystem controls, the notion of complete immunity is not only false but actively dangerous, lulling millions of users into a false sense of security that cybercriminals are eager to exploit.
The Origins of the “Macs Don’t Get Viruses” Belief
Understanding why this myth took hold requires a brief look at computing history. The belief was not born from nothing — it had a foundation in real-world conditions that have since fundamentally changed.
- Market Share as a Shield: For most of the 1990s and 2000s, Windows dominated the personal computing market with upwards of 90% market share according to historical IDC and StatCounter data. From a purely economic standpoint, malware authors prioritized Windows because attacking it yielded the greatest return. Writing Mac-specific malware was a low-ROI endeavor. This statistical reality was mistakenly interpreted as a technical immunity.
- Unix-Based Architecture: When Apple transitioned macOS (then OS X) to a Unix foundation with the release of Mac OS X 10.0 in 2001, it inherited a permissions-based security model that genuinely made certain classes of attack harder to execute. Standard user accounts lacked the root-level privileges needed to make system-wide changes, adding a meaningful barrier to self-propagating worms that plagued Windows XP-era systems.
- Apple’s Controlled Ecosystem: The introduction of the Mac App Store in 2011 and the progressive hardening of Gatekeeper — Apple’s mechanism for verifying application signatures — created a curated distribution channel that filtered out a large percentage of malicious software before it could reach end users. These were real protections, and they worked well in their era.
The Modern Reality: A Surging Threat Landscape
The conditions that once made Macs a low-priority target have dramatically shifted. Apple’s resurgent market share, the premium demographics of its user base, and the sheer sophistication of modern threat actors have converged to create a threat landscape that no Mac user can afford to ignore.
- Documented Malware Families: The security community has catalogued numerous significant Mac-specific threats in recent years. Silver Sparrow, discovered in early 2021, infected nearly 30,000 Macs globally and was notable for targeting Apple’s then-new M1 Silicon chips — demonstrating that even cutting-edge hardware provides no immunity. XCSSET targeted Mac developers by injecting malicious code into Xcode projects, turning legitimate software development pipelines into malware delivery systems. Shlayer, a persistent adware trojan, was identified by Kaspersky as the most widespread Mac threat for multiple consecutive years, infecting an estimated one in ten Mac users at its peak. According to a 2025 Malwarebytes Threat Intelligence Report, year-over-year detections of Mac-specific malware and potentially unwanted programs (PUPs) have continued their upward trajectory, with adware and data-stealing trojans leading the surge.
- High-Value Target Demographics: Macs are disproportionately used by professionals, creative agencies, financial services workers, and technology executives — precisely the demographics that cybercriminals find most lucrative. A successful attack on a Mac user is statistically more likely to yield valuable intellectual property, financial credentials, or access to corporate networks than a comparable attack on the average Windows home user.
- Accelerating Market Share: Apple’s Mac market share has grown substantially, with 2025 figures from IDC placing it consistently above 15% in the premium PC segment globally. As the addressable audience grows, the economic calculus for malware authors shifts decisively in favor of investing in Mac-specific attack tooling.

How Do Macs Get Infected? Common Attack Vectors Explained
Mac infections rarely happen by magic or through some mysterious technical exploit that users have no agency over. In the overwhelming majority of documented cases, infections occur through specific, identifiable pathways — many of which rely heavily on deceiving the user rather than defeating the operating system. Understanding these vectors is the first step toward neutralizing them.
Social Engineering and Deceptive Downloads
The human element remains the most exploited vulnerability in any security system. Cybercriminals have become extraordinarily skilled at manufacturing trust and urgency to bypass rational judgment.
- Fake Software Updates and Cracked Applications: One of the most enduring and effective delivery mechanisms for Mac malware is the fake software update prompt. Malicious websites display convincing pop-ups claiming that your Adobe Flash Player, browser, or macOS system is critically out of date and must be updated immediately. The “update” is, of course, a malware installer. Similarly, websites distributing “cracked” or pirated versions of popular productivity software (video editors, design tools, office suites) routinely bundle their payloads with trojans, keyloggers, or cryptominers. The user willingly circumvents Gatekeeper by manually approving the installation, negating Apple’s primary defense.
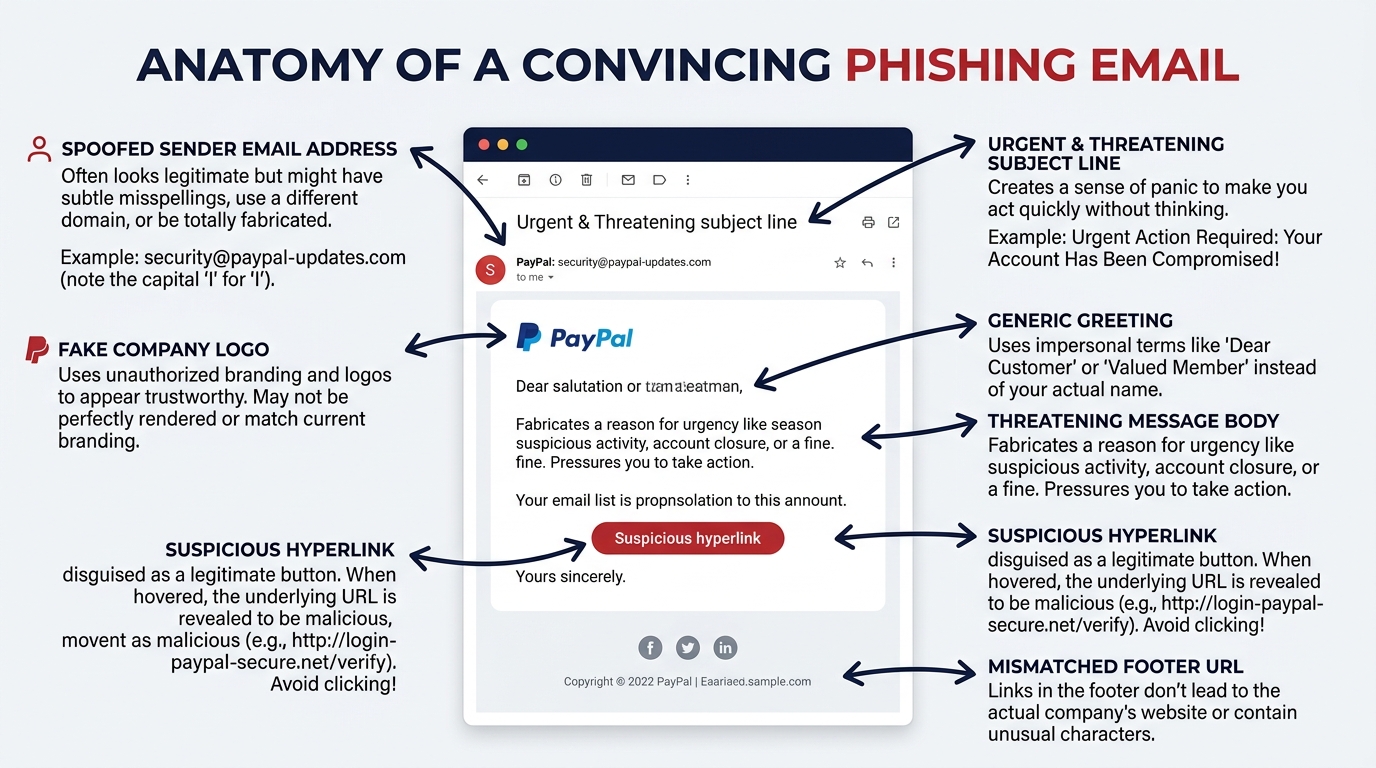
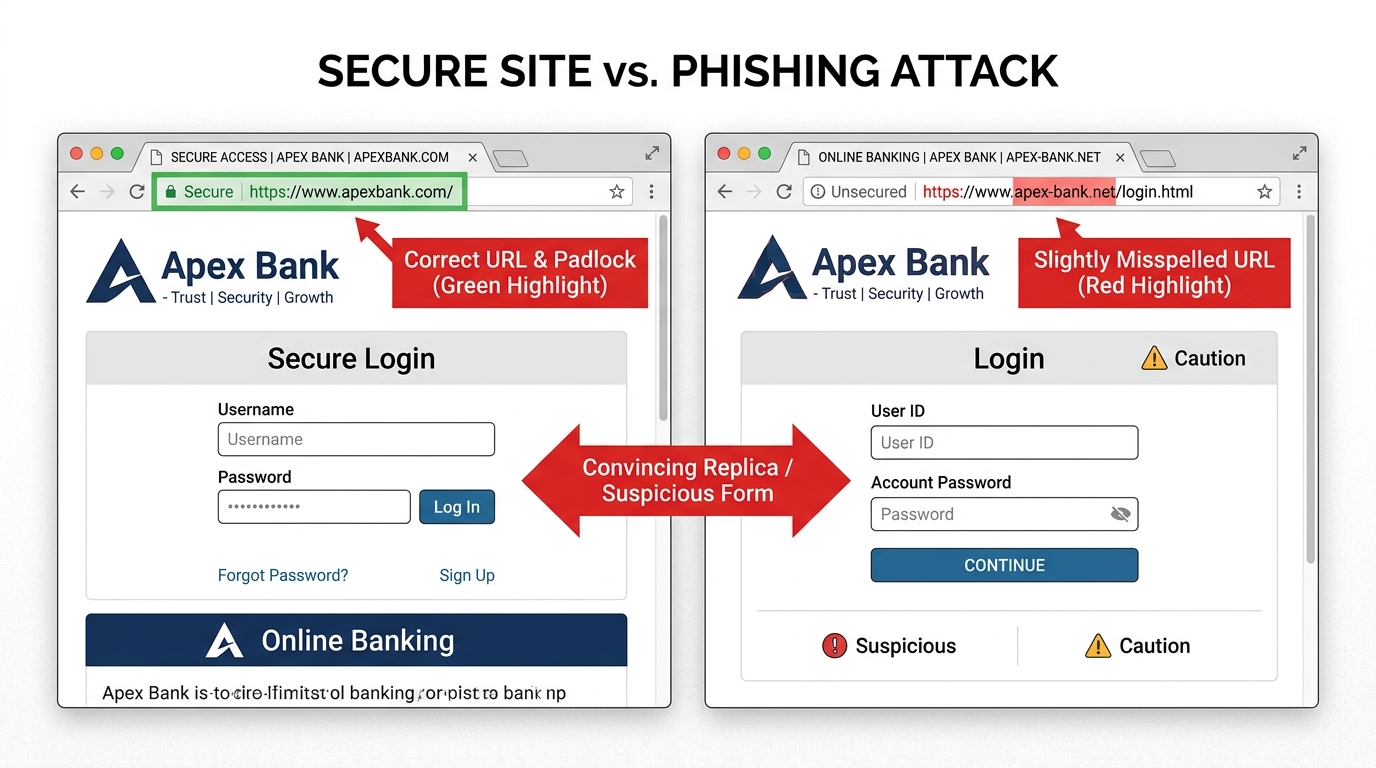
- Phishing via Email and Malicious Websites: Phishing attacks targeting Mac users have grown in sophistication and volume. Attackers craft emails that convincingly impersonate Apple Support, financial institutions, or cloud service providers, directing users to pixel-perfect replica login pages designed to harvest credentials. A 2026 Cybersecurity Ventures report projected that phishing would remain the number-one initial access vector for Mac-targeted attacks, accounting for over 60% of reported incidents.
- Malvertising: Malicious advertising — the embedding of malware-laden code within legitimate advertising networks — can expose Mac users to drive-by download attempts simply by visiting reputable, high-traffic websites. The user does not need to click anything; merely loading the page with a vulnerable browser or plugin can initiate the infection chain.

Exploiting Software Vulnerabilities and Legitimate Tools
Beyond social engineering, a technically sophisticated class of attacks targets the software stack itself, exploiting flaws that exist independently of user behavior.
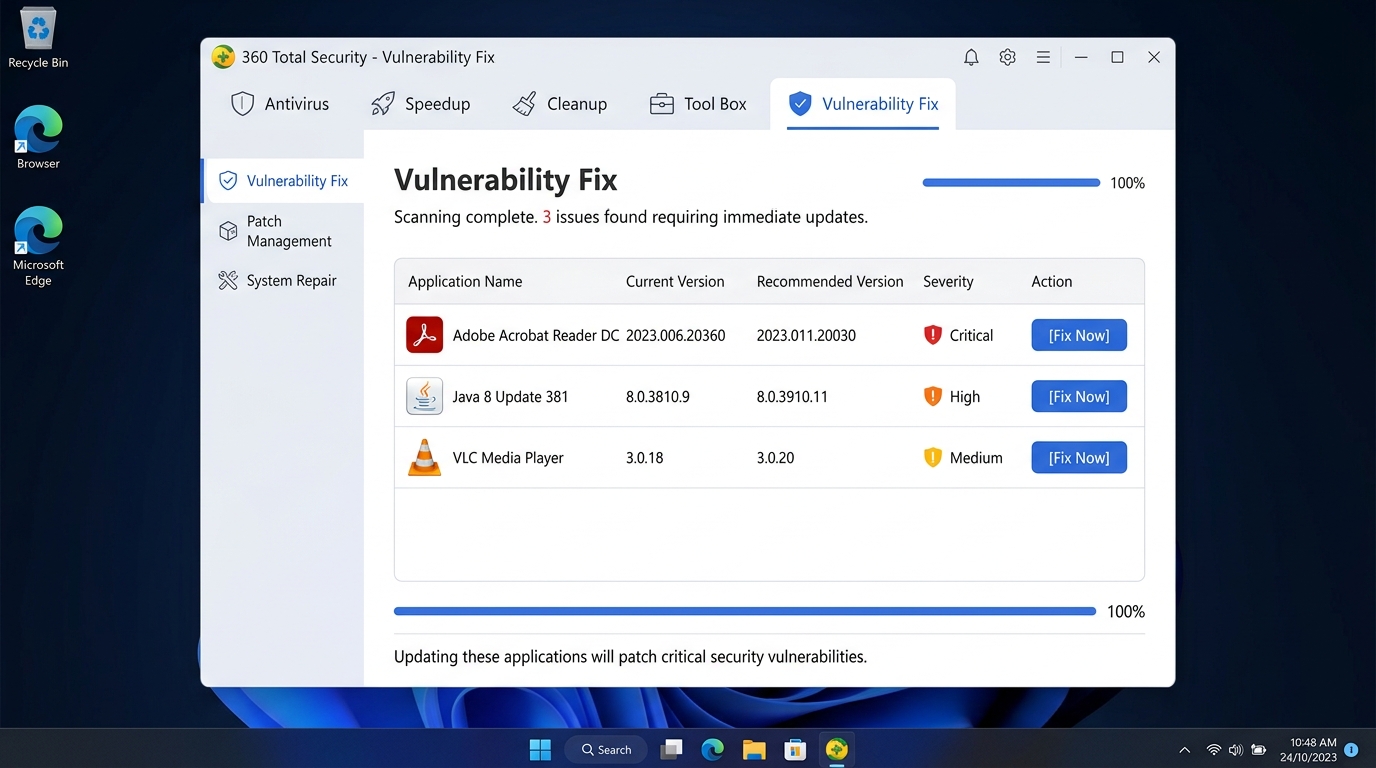
- Unpatched Vulnerabilities: Every piece of software — macOS itself, Safari, Chrome, Firefox, Adobe Reader, Java — contains security vulnerabilities. Apple and third-party developers release patches to address these flaws, but the window between vulnerability disclosure and patch deployment is a prime hunting ground for attackers. A 2025 analysis by the Zero Day Initiative found that macOS and its bundled applications accounted for a significant and growing share of high-severity CVEs (Common Vulnerabilities and Exposures) disclosed annually.
- Living off the Land (LotL) Techniques: A particularly insidious class of attack involves abusing legitimate, trusted macOS system tools to execute malicious commands. Attackers use built-in scripting environments like AppleScript, Python, osascript, and bash to perform reconnaissance, establish persistence, and exfiltrate data — all without ever introducing a traditional malware binary that security scanners might flag. Because these activities use signed, trusted system components, they are significantly harder to detect.
| Attack Vector | Typical Delivery Method | User Behavior That Enables It |
|---|---|---|
| Fake Software Update | Malicious website pop-up or redirect | Manually approving and running an unsigned installer |
| Cracked/Pirated Software | Third-party torrent or warez sites | Deliberately bypassing Gatekeeper warnings |
| Phishing Email | Spoofed email with malicious link or attachment | Clicking links without verifying sender authenticity |
| Malvertising | Compromised ad network on legitimate site | Using an unpatched browser or outdated plugins |
| Unpatched Vulnerability Exploit | Drive-by download or network-based attack | Delaying macOS and application security updates |
| Living off the Land (LotL) | Malicious script delivered via phishing or download | Granting excessive permissions to applications |
What Are the Signs Your Mac Might Have a Virus or Malware?
Early detection is critical. The longer malware operates undetected on a system, the more damage it can cause — whether that means exfiltrating sensitive data, mining cryptocurrency at your expense, or establishing a persistent backdoor for future exploitation. Mac malware is often designed to operate quietly, but it almost always leaves behavioral fingerprints that an informed user can recognize.
Performance and System Anomalies
Your Mac’s performance is one of its most reliable health indicators. Sudden, unexplained changes in how your system behaves are among the earliest and most actionable warning signs.
- Unexplained Slowdowns and Thermal Stress: If your Mac suddenly feels sluggish, your fans are running at high speed under light workloads, or your MacBook’s battery is draining significantly faster than usual, a background process may be consuming substantial CPU or GPU resources. Cryptomining malware, in particular, is notorious for maxing out processor utilization to generate cryptocurrency for the attacker at your hardware’s expense.
- Application Instability: Frequent, unexpected application crashes or system freezes that were not previously occurring can indicate that malware has corrupted system files, injected code into running processes, or is competing aggressively for system resources.
- Unauthorized Applications and Login Items: Regularly auditing your Applications folder and your System Settings > General > Login Items list is a simple but powerful detection technique. Malware frequently installs helper applications or launch agents that run automatically at startup. Any entry you do not recognize warrants immediate investigation.
Browser and Network Red Flags
Many of the most common Mac threats — adware, browser hijackers, and data-stealing trojans — manifest most visibly through changes to browser behavior and unusual network activity.
- Browser Hijacking: If your browser’s homepage, new tab page, or default search engine has changed to an unfamiliar service without your deliberate action, you are almost certainly dealing with a browser hijacker. These threats typically install as browser extensions and redirect your searches through ad-laden, potentially malicious proxy search engines to generate revenue for their operators.
- Abnormal Pop-Up Advertising: A sudden influx of pop-up advertisements — particularly those appearing on websites that have never displayed them before, or ads with explicit, alarming, or off-topic content — is a classic symptom of adware infection. Adware injects advertising code into web traffic at the system level, meaning it affects all browsers simultaneously.
- Suspicious Network Activity: macOS’s built-in Activity Monitor (found in Applications > Utilities) provides a real-time view of network data sent and received by each process on your system. Navigate to the Network tab and sort by “Sent Bytes” or “Rcvd Bytes.” Any process you do not recognize that is transmitting significant volumes of data — especially to IP addresses in unexpected geographic regions — should be treated as a serious red flag and investigated immediately.
To check for suspicious network activity in Activity Monitor, follow these steps:
# Steps to Investigate Suspicious Network Activity on macOS
1. Open Finder > Applications > Utilities > Activity Monitor
2. Click the "Network" tab at the top of the window
3. Click "Sent Bytes" column header to sort by outgoing data (descending)
4. Look for unfamiliar process names with high data transmission values
5. Right-click any suspicious process and select "Inspect" for more details
6. Cross-reference unknown process names at: https://www.virustotal.com/Proactive Defense: Essential Steps to Protect Your Mac
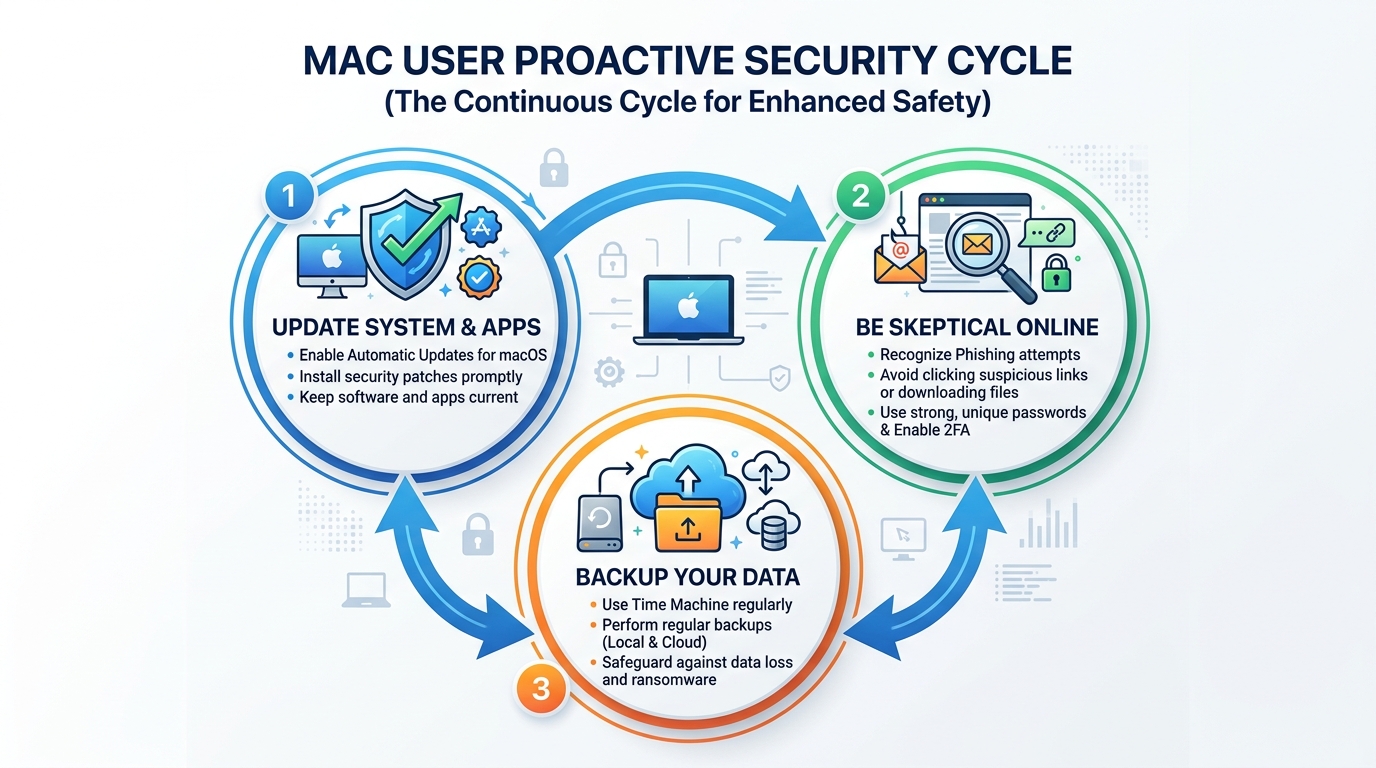
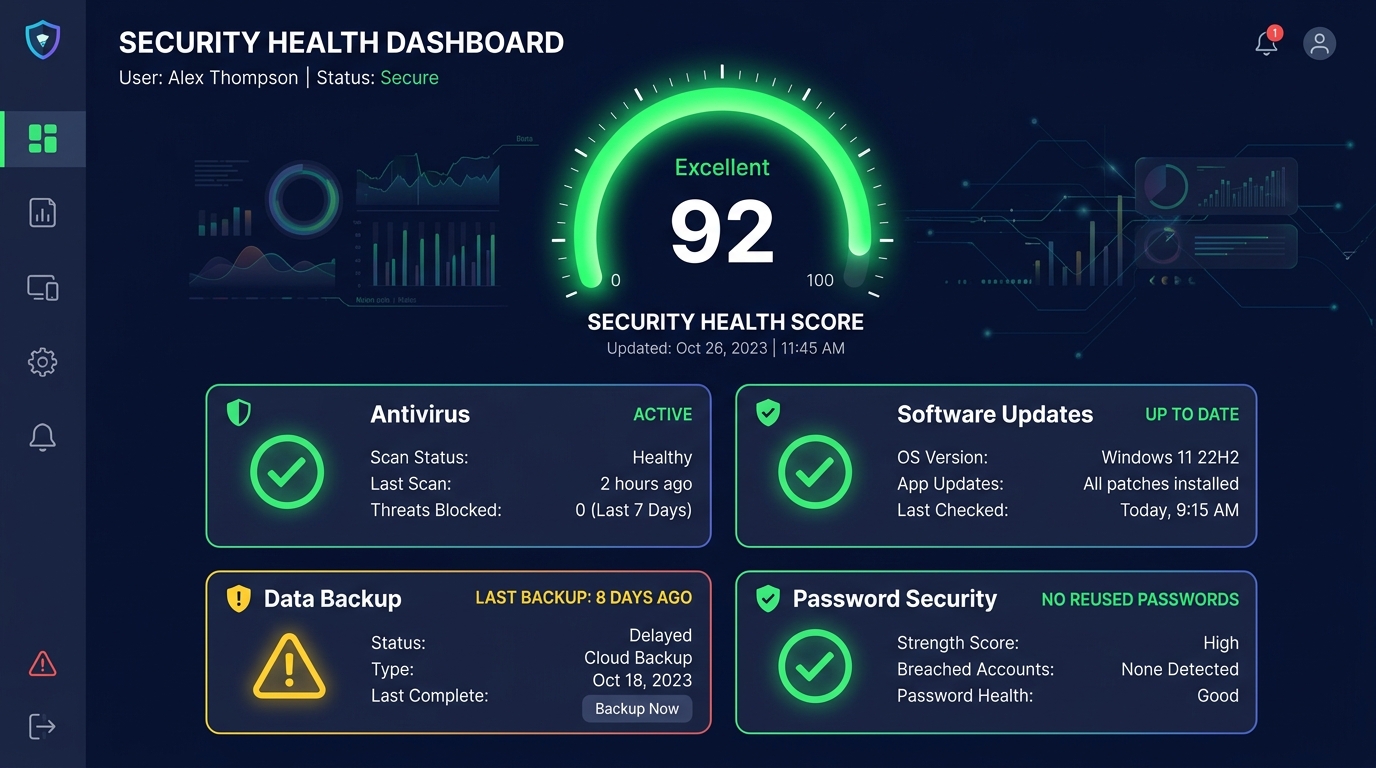
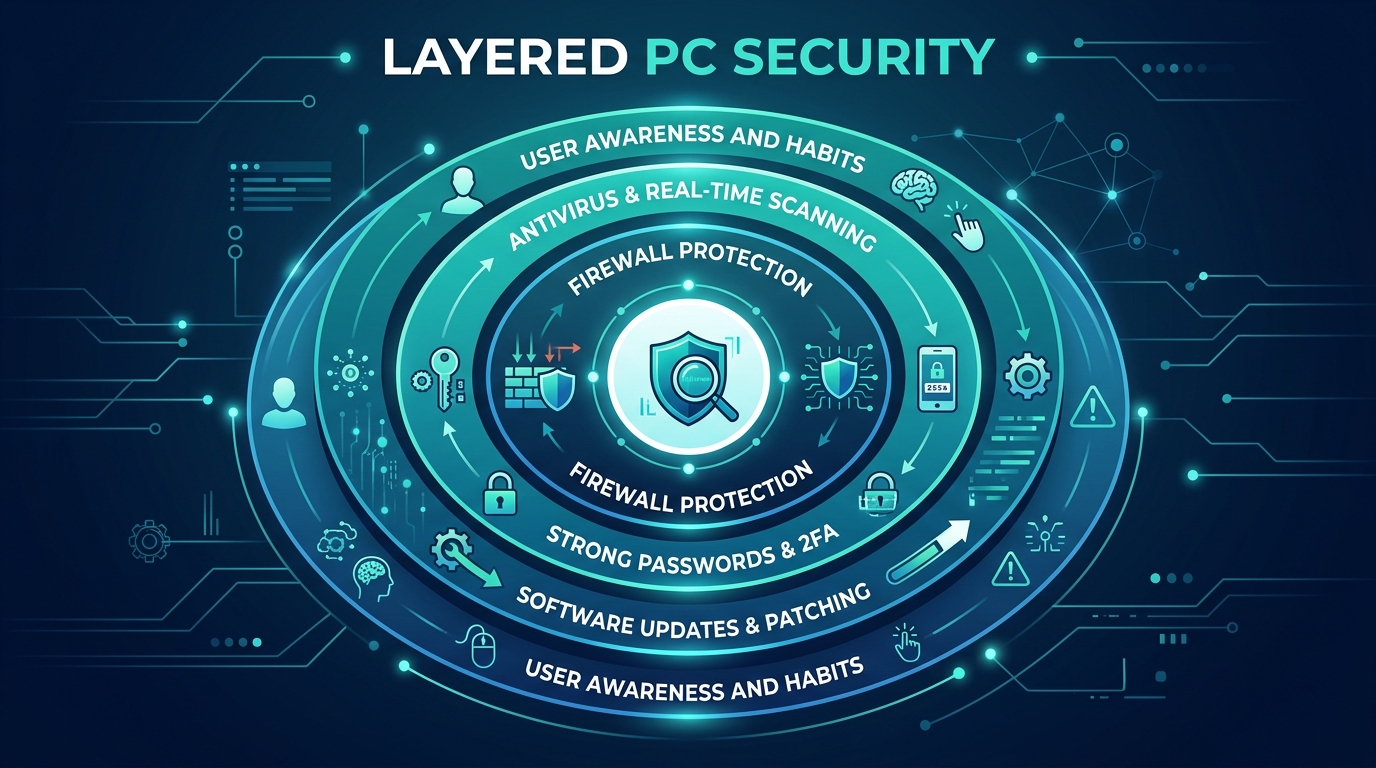
Effective Mac security is not a single action but a layered system — a defense-in-depth strategy where multiple overlapping controls compensate for each other’s limitations. No single tool or habit provides complete protection; the combination of Apple’s built-in features, disciplined user behavior, and supplemental security software creates a substantially more resilient posture than any one layer alone.
Maximizing Apple’s Built-in Security Features
Apple has invested significantly in macOS security infrastructure. These tools are free, already installed, and highly effective when properly configured — yet many users leave them underutilized or misconfigured.
- Gatekeeper Configuration: Ensure Gatekeeper is set to its recommended security level by navigating to System Settings > Privacy & Security and confirming that “App Store and identified developers” is selected under the “Allow applications downloaded from” section. This setting requires all applications to be either from Apple’s curated App Store or signed with a valid Apple Developer certificate — blocking the vast majority of unsigned malware installers.
- Enable the macOS Firewall: Navigate to System Settings > Network > Firewall and ensure it is turned on. The macOS firewall controls which applications are permitted to accept incoming network connections, providing a meaningful barrier against network-based intrusion attempts and unauthorized remote access tools.
- Prioritize System and Software Updates: This is, without qualification, the single most impactful security action available to any Mac user. Navigate to System Settings > General > Software Update and enable automatic updates. “The number one entry point for successful attacks against macOS systems is unpatched software,” according to a 2025 analysis by security researchers at Objective-See, a leading macOS security research organization. “The time between a vulnerability being disclosed and it being actively exploited in the wild has shrunk from months to days. Automatic updates are no longer optional — they are essential.”
# Verify Gatekeeper Status via Terminal (macOS)
spctl --status
# Expected output: assessments enabled
# Enable Gatekeeper if disabled
sudo spctl --master-enable
# Verify macOS Firewall Status via Terminal
/usr/libexec/ApplicationFirewall/socketfilterfw --getglobalstate
# Expected output: Firewall is enabled. (State = 1)Cultivating Safe Computing Habits
Technology controls are only as effective as the human behaviors operating within them. Disciplined habits form the behavioral layer of your security stack.
- Source Integrity for Downloads: Adopt a strict policy of only downloading software from the official Mac App Store or directly from verified developer websites. If a search engine result leads you to a third-party download mirror for software you are seeking, treat it with extreme suspicion. The official developer’s website URL should be verifiable through multiple independent sources.
- Healthy Skepticism Toward Communications: Treat every unsolicited email, direct message, or social media communication containing a link or attachment as potentially malicious — even if it appears to originate from a known contact, as email spoofing and account compromise are common. Verify unexpected requests through a separate, trusted communication channel before acting on them.
- Credential Hygiene and 2FA: Use a reputable password manager to generate and store unique, high-entropy passwords for every account. Enable Two-Factor Authentication (2FA) on all services that support it, particularly Apple ID, email, banking, and cloud storage. Even if a phishing attack successfully captures your password, 2FA provides a critical second barrier against account takeover.
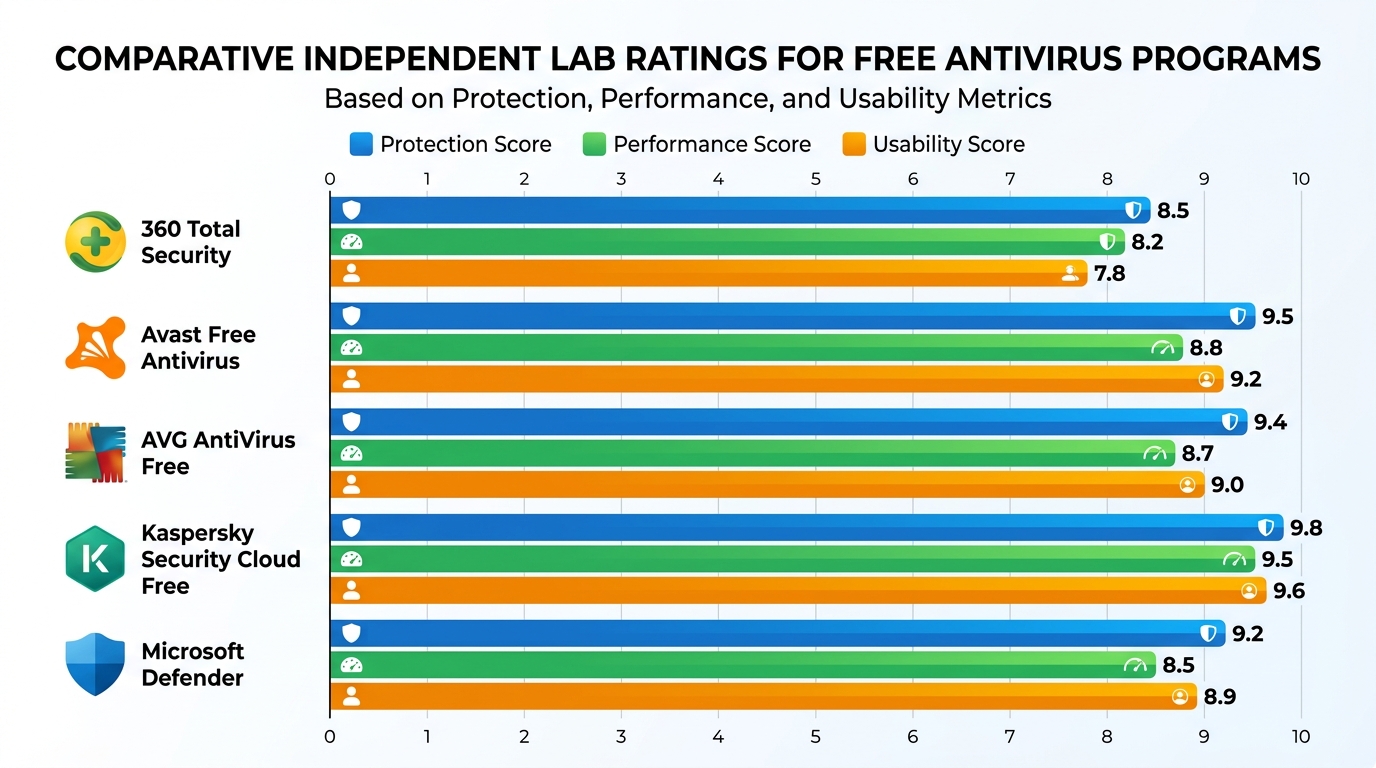
Why Consider a Dedicated Security Solution Like 360 Total Security for Mac?
Apple’s native security tools — Gatekeeper, XProtect, Malware Removal Tool (MRT), and the Firewall — are genuinely capable and form an important foundation. However, they have documented limitations: XProtect’s signature database is updated less frequently than dedicated commercial security products, it offers no real-time behavioral monitoring, and it provides no system optimization, cleanup, or proactive web protection capabilities. For users who demand comprehensive, layered protection, a dedicated security suite fills these gaps decisively.
Beyond Basic Scanning: Multi-Layered Real-Time Protection
360 Total Security for Mac is engineered to complement and substantially extend macOS’s native defenses through several interconnected protection layers.
- Real-Time File System Monitoring: Unlike XProtect, which performs checks primarily at application launch, 360 Total Security continuously monitors the file system in real time. Every file you download, every document you open, and every application you execute is scanned against an up-to-the-minute threat database before it can interact with your system. This proactive interception model stops threats at the point of entry rather than after they have already executed.
- Cloud-Based AI Detection Engine: 360 Total Security leverages a cloud-connected artificial intelligence detection engine — what the company calls its “security brain” — that can identify new, previously unseen malware variants based on behavioral patterns and structural analysis rather than relying solely on known malware signatures. This capability is particularly critical for defending against zero-day threats and novel malware families like Silver Sparrow, which evaded detection by traditional signature-based tools for an extended period after deployment.
- Web and Phishing Protection: The integrated web protection module actively blocks access to known phishing websites, malicious download portals, and fraudulent banking pages directly within your browser. This provides a critical safety net for the moments when social engineering is most likely to succeed — when a user is actively engaged with a convincing, urgent-seeming deception.
Comprehensive Cleanup and Performance Boosting
One of 360 Total Security’s most practically valuable differentiators is its dual role as both a security tool and a system health optimizer — addressing the performance symptoms that malware often causes, as well as the general system bloat that accumulates over time.
- Malware Removal and Adware Cleanup: For systems that may already be compromised, 360 Total Security’s deep scan capabilities are designed to find and fully remove entrenched malware, adware, browser hijackers, and Potentially Unwanted Programs (PUPs) that native tools and lighter scanners frequently miss. This includes cleaning up the persistent launch agents, browser extensions, and configuration profile modifications that many adware families use to survive reboots and manual removal attempts.
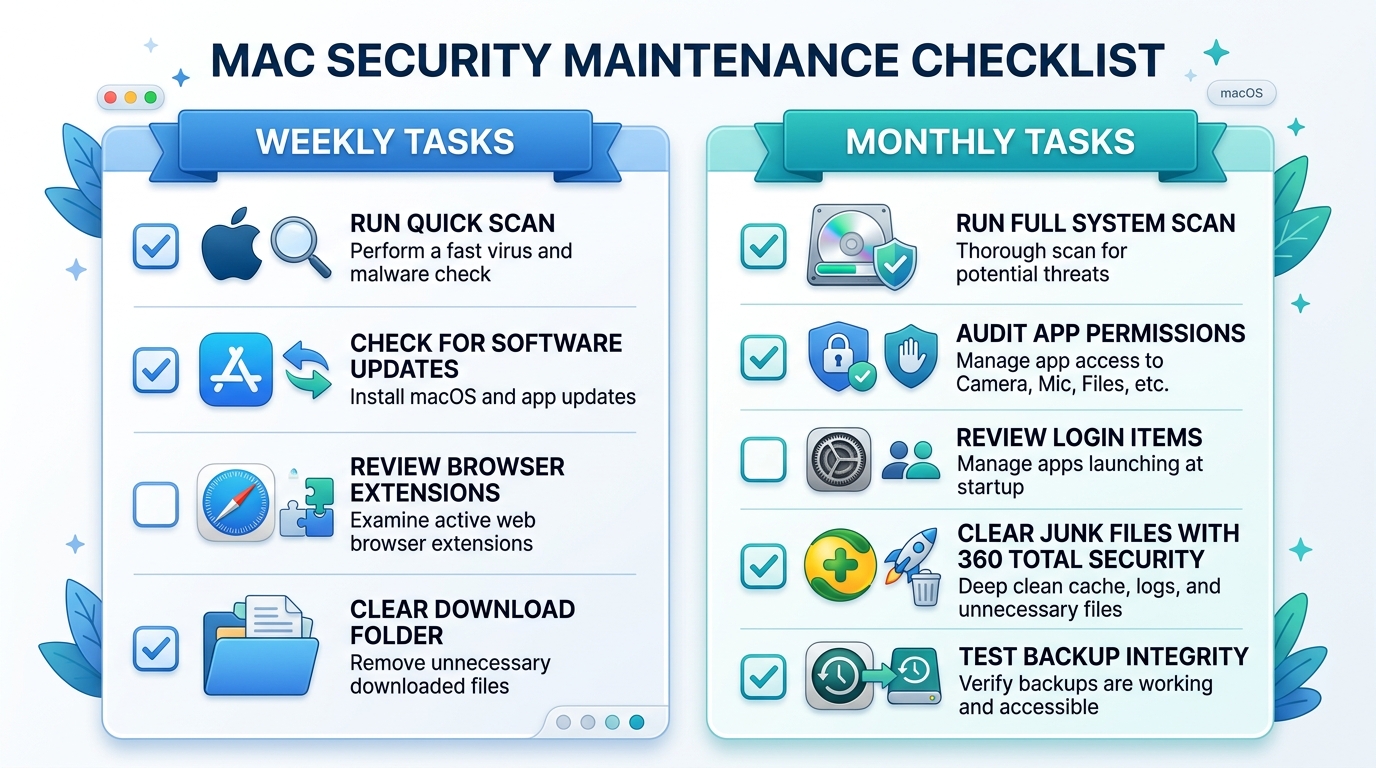
- System Optimization Suite: The built-in optimization tools include a junk file cleaner that removes system caches, application residuals, and temporary files; a startup manager that identifies and helps you disable unnecessary login items that slow boot times; and a large file finder that surfaces storage-consuming files you may have forgotten. These tools directly address the performance degradation that is both a symptom of malware and a general consequence of long-term Mac use.
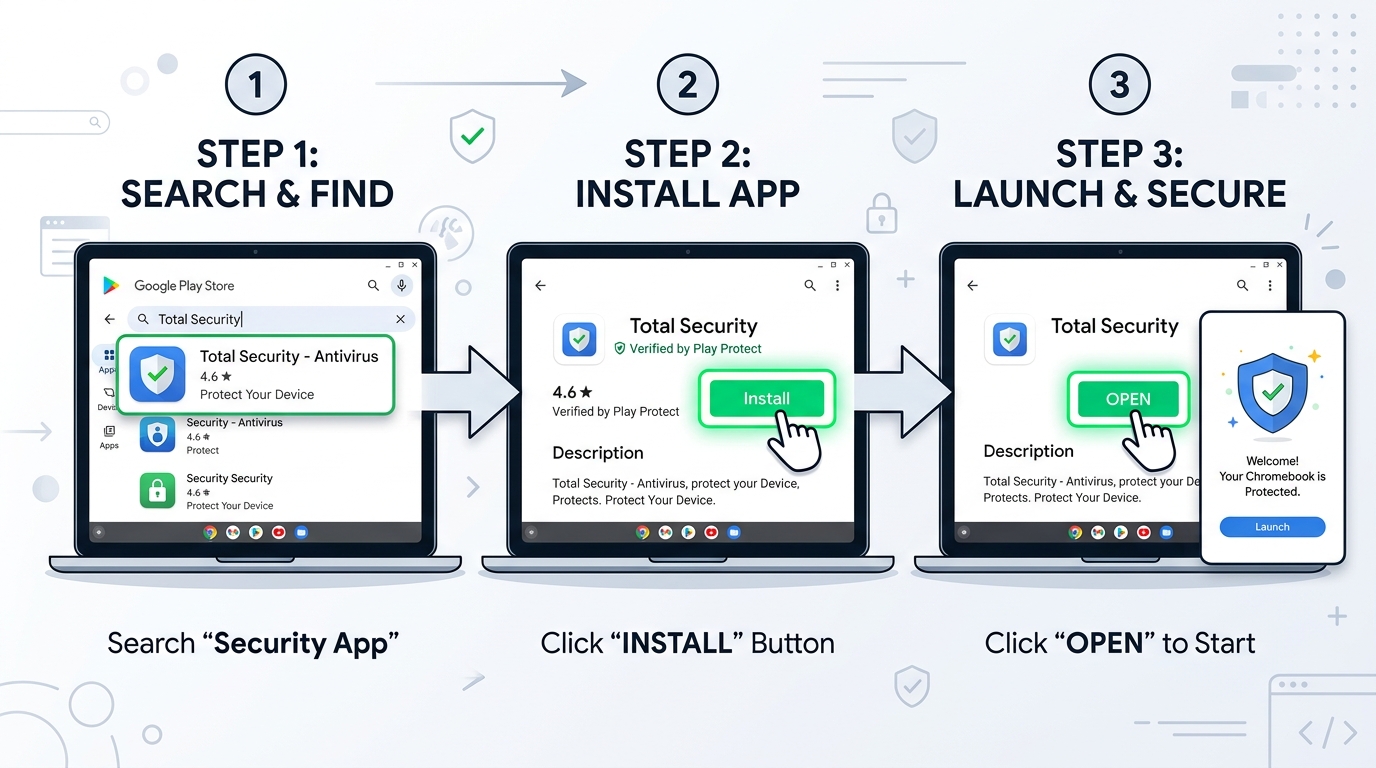
Getting started with 360 Total Security on your Mac is straightforward:
# How to Get Started with 360 Total Security for Mac
1. Visit the official website: https://www.360totalsecurity.com/en
2. Download the macOS installer (.dmg file) from the official download page
3. Open the .dmg file and drag 360 Total Security to your Applications folder
4. Launch the application and grant the required system permissions
(Full Disk Access, Notifications) in System Settings > Privacy & Security
5. Run an initial Full Scan to establish a security baseline
6. Enable Real-Time Protection in the application settings
7. Schedule weekly scans for ongoing maintenanceFinal Verdict and Actionable Security Checklist
The evidence is unambiguous: Macs are not immune to viruses, malware, adware, or any other class of modern cyber threat. The myth of Mac immunity is a historical artifact that has outlived the conditions that gave rise to it. However, this reality should not be cause for alarm — it should be cause for informed, structured action. The threat to Mac users is real but entirely manageable with the right combination of awareness, habits, and tools.
Your Mac Security Priority Checklist
- Immediate Action — Run a Baseline Scan: If you have never run a dedicated security scan on your Mac, do it today. Download 360 Total Security — it is available at no cost and requires no commitment — and run a full system scan to establish a clean baseline. You may be surprised by what it finds, particularly if you have been operating under the assumption that your Mac was inherently safe.
- Habit Formation — Source Discipline: Commit, starting today, to downloading software exclusively from the Mac App Store or directly verified developer websites. Extend this discipline to a healthy skepticism toward all unsolicited links and email attachments. These two behavioral changes alone eliminate the delivery mechanism for the majority of Mac infections.
- System Hygiene — Enable Automatic Updates: Turn on automatic macOS updates, enable the Firewall, and set a monthly calendar reminder to review your Login Items and Applications folder for anything unfamiliar. These routine hygiene practices close the vulnerability windows that attackers depend on.
Embracing a Security-Aware Mindset
The final and perhaps most important shift is cognitive. Acknowledging that your Mac faces real threats is not an admission of Apple’s failure — it is a recognition of the reality that no operating system exists in isolation from the evolving tactics of a global, financially motivated cybercriminal ecosystem.
- Vigilance Is Your Most Powerful Tool: The majority of successful Mac attacks require the user to make a mistake — to click the wrong link, approve the wrong installer, or ignore a warning. An informed, skeptical user dramatically reduces the attack surface available to any threat actor.
- Security Software as a Performance Enhancer: Reframe how you think about security software. Tools like 360 Total Security are not a sign that macOS is weak — they are a performance and maintenance enhancer that removes junk, catches what native tools miss, and keeps your system running at its best. They complement macOS’s strengths rather than compensating for fundamental weaknesses.
| Common Myth | Evidence-Based Reality | Recommended Action |
|---|---|---|
| “Macs cannot get viruses” | Thousands of Mac malware families are actively documented and deployed | Run a full scan with 360 Total Security |
| “Apple’s built-in tools are sufficient” | XProtect has limited real-time monitoring and no web protection or cleanup tools | Supplement with a dedicated security suite |
| “I only visit safe websites, so I’m fine” | Malvertising and phishing operate on legitimate, high-traffic websites | Enable web protection; use an ad blocker |
| “Slow Mac = old hardware” | Performance degradation is a primary malware symptom | Scan for malware; use optimization tools |
| “Security software slows down my Mac” | Modern security suites include optimization tools that improve performance | Try 360 Total Security’s free optimization features |
The bottom line: treat your Mac with the same security discipline you would apply to any valuable, internet-connected computing device. The myth of immunity is over. The era of informed, proactive Mac security has begun. Visit 360 Total Security today to take your first concrete step toward comprehensive Mac protection.
Frequently Asked Questions
Can a Mac really get a virus, or is that just a myth?
Yes, Macs can absolutely get viruses, trojans, adware, ransomware, and other forms of malware. The belief that they cannot is a myth rooted in historical conditions — primarily lower market share — that no longer apply. Security firms including Malwarebytes, Kaspersky, and Objective-See have documented thousands of Mac-specific malware families, and the number of detected threats continues to grow year over year. No operating system is inherently immune to all threats.
Does macOS have built-in antivirus protection?
Yes, macOS includes several native security mechanisms: XProtect (a signature-based malware scanner), the Malware Removal Tool (MRT), Gatekeeper (application verification), and a system Firewall. These tools provide a meaningful baseline of protection. However, XProtect’s signatures are updated less frequently than commercial products, it lacks real-time behavioral monitoring, and it provides no web protection or system cleanup capabilities — gaps that dedicated solutions like 360 Total Security are designed to fill.
What is the most common way Macs get infected with malware?
The most common infection vector for Mac malware is social engineering — specifically, fake software update prompts and installers for pirated applications that bundle malware payloads. These attacks work by convincing users to manually approve and run malicious software, effectively bypassing Gatekeeper. Phishing emails and malvertising on legitimate websites are the second and third most common vectors. The consistent theme is that most Mac infections require a user to take an action, making informed behavior the most powerful preventive measure.
How can I tell if my Mac already has malware?
Key warning signs include: unexplained performance slowdowns or excessive fan activity under light workloads; browser homepage or search engine changes you did not make; an influx of pop-up advertisements across all websites; unfamiliar applications in your Applications folder or Login Items; and unusual network activity visible in Activity Monitor. If you observe any of these symptoms, run a full scan with a dedicated security tool like 360 Total Security immediately.
Is 360 Total Security free for Mac, and what does it include?
360 Total Security offers a free tier for macOS that includes full virus and malware scanning, real-time file system protection, and system optimization tools including junk file cleaning and startup management. A premium tier with expanded features including enhanced web protection and priority cloud scanning is also available. The free version represents a zero-cost, zero-risk starting point for any Mac user looking to establish a security baseline and is available for download at the 360 Total Security official website.
About the Author: This article was researched and written by a Senior Technical Writer specializing in cybersecurity, endpoint protection, and macOS security architecture. With over a decade of experience translating complex security concepts for both technical and general audiences, the author has contributed to cybersecurity publications, enterprise security documentation, and consumer education initiatives focused on practical, evidence-based digital safety guidance.